The 15-Rotor Cipher That Defeated Every Codebreaker in World War II
April 1, 1930, Washington, DC. A young mathematician named Frank Rowlet walked into a cramped office at the Army’s Signal Intelligence Service for his first day of work. His boss, William Freriedman, handed him an impossible assignment. Create paper tapes with random sequences to control a new cipher machine.
Not just a few tapes, thousands of them. Maybe tens of thousands. For nearly four years, Rowlet struggled. The concept was brilliant, but the execution was a nightmare. Producing truly random sequences was extraordinarily difficult. Distributing hundreds of thousands of paper tapes to military units around the world nearly impossible, and [snorts] operators would need to change these tapes constantly, creating massive logistical chaos.
Finally, in May 1934, Rowlet had enough. He threatened to quit unless Freriedman would listen to his alternative idea. What happened next would create the only cipher machine in World War II that was never broken by enemy codereakers. Not the Germans, not the Japanese, nobody. While Britain’s Enigma fell to brilliant mathematicians at Bletchley Park, while Japan’s purple cipher was cracked by American cryp analysts, one machine remained absolutely impenetrable, the Sigaba.
And the story of how it came to exist involves a near fist fight between two cryptographers, stolen ideas, interervice rivalry, women assembling 450,000 individually wired rotors, and a 40 lb thermite bomb strapped to every army machine. This is the engineering story of the cipher machine that protected every secret from D-Day planning to President Roosevelt’s conversations with Winston Churchill.
To understand why sagaba was revolutionary, we need to understand the problem it solved. In the early 1920s, a man named Edward Heburn had a brilliant idea while sitting in jail for horse theft. [snorts] He realized that cipher machines didn’t need to print the same letter you typed. If you wired a typewriter so the keys connected to different letters and if that wiring changed with every keystroke, you’d have an incredibly strong cipher.
His solution was elegant rotating discs called rotors. Each rotor had 26 electrical contacts on both sides connected by wires running through the disc in scrambled patterns. As you typed, the first rotor would advance one position, changing which letter connected to which. After 26 letters, the second rotor would advance one position.

After 676 letters, the third would move. Heburn was a horse thief, not a cryptographer. The US Army Signal Intelligence Service immediately saw the fatal weakness. The rotors moved in a completely predictable pattern. First rotor, one step. Every 26 keystrokes, second rotor, one step. Every 676 keystrokes, third rotor, one step. Predictable movement meant professional code breakers could exploit mathematical patterns in the encrypted text.
If you knew when each rotor moved, you could work backwards to figure out the internal wiring. The Germans saw this, too. Arthur Sherbius improved Heburn’s design, creating the Enigma machine with a plug board that scrambled some of the letters before they even entered the rotors. The result was stronger, more compact, and easier to use.
The German military adopted it enthusiastically. But Enigma still had the same fundamental weakness. Regular predictable rotor movement. By 1930, William Freriedman, chief of the newly created signal intelligence service, understood the core problem. The strength of rotor machines came from changing the electrical path with every letter.
The weakness came from doing it predictably. His solution was radical. make rotor movement completely random and unpredictable. Freriedman’s concept involved paper tapes with holes punched in random sequences. The machine would read the tape and move the rotors according to the random instructions. One letter might advance three rotors.
The next might not move at all. Another might advance just one but a different one than before. Mathematically, it was nearly perfect. Operationally, it was a disaster. Frank Rowlet spent nearly four years trying to make Freriedman’s paper tape system work. He was 26 years old when he started, hired straight out of college, and tasked with producing thousands upon thousands of random number sequences.
First problem, humans are terrible at generating truly random numbers. Even trained mathematicians unconsciously create patterns. Rowlet would need mechanical assistance to generate cryptographically sound randomness. Second problem, physical production. Each paper tape needed to be punched with thousands of holes in precise positions.
Any error made that tape useless. The volume required was staggering. Third problem, distribution. Every military unit using the system would need identical copies of the same tapes, shipping hundreds of thousands of fragile paper tapes around the world, keeping them organized, ensuring they arrived undamaged and remained synchronized across thousands of operators.
The logistics were impossible. Fourth problem, operational security. Operators would need to switch tapes constantly. Every tape switch was an opportunity for error, for loss, for capture by the enemy. But Rowlet couldn’t make Freriedman understand. His boss was convinced the mathematical elegance of the system proved it would work.
Operational difficulties could be overcome with better training and discipline. By May 1934, Rowlet had reached his breaking point. He told Freriedman he would quit unless they had a serious conversation about an alternative approach. That got Freriedman’s attention. Rowlet explained his breakthrough. While struggling to generate random sequences for the paper tapes, he’d realized something profound.
You could use an ordinary rotor machine to generate pseudo random numbers. But if you had a rotor machine generating pseudo random numbers anyway, why not just use those rotors to directly control another set of rotors? Instead of paper tapes, control signals, cipher rotors, you’d have control rotors, control signals, cipher rotors.
Freriedman listened in silence. Then he told Rowlet to leave his office. He didn’t speak to him for the rest of the day. Rowlet prepared to be fired. The next morning, Freriedman called Rowlet into his office and told him to stop all work on the paper tape system. They would pursue Rowlet’s design instead.
Within months, they had a complete design. The machine would use 15 rotors in three banks of five. The cipher rotors would actually encrypt the message. The control rotors would determine how the cipher rotors moved. and index rotors would add another layer of complexity to the control signals. The result, movement patterns so complex, so unpredictable that even knowing the machine’s design wouldn’t help you break the code without knowing the exact starting positions and wirings of all 15 rotors. They named it SIGABA.
The SIG designated it for cryptographic signals work. The ABA was completely random, deliberately meaningless to prevent enemies from inferring anything from the name. But now they faced a different problem, the US Navy. While the army was developing Sagaba, the Navy’s cryptographers were fighting a desperate battle.
They were being pressured to purchase large quantities of Heburn rotor machines, the same devices they knew were fundamentally insecure. The Navy’s cryptographic budget was fixed. If they spent it on Heburn machines, there would be no money for anything better. But unless they could present a viable alternative, they’d be forced to buy the machines anyway to equip the fleet.
Captain Joseph Winganger, head of naval intelligence, did something unprecedented. He asked the army for help. Interservice cooperation in the 1930s was virtually unheard of. The army and navy competed fiercely for budget, for prestige, for credit. Asking your rival service for assistance was humiliating, but Winger had no choice.
Freriedman immediately arranged for Rowlet to present Sagaba to a large group of Navy personnel. Rowlet explained every detail of the design, the mathematics, the operational procedures. Winganger sat through the entire presentation without expression. He asked no questions. He made no comments. Then nothing. Weeks passed, then months.
Whenever Freriedman inquired about the Navy’s decision, Wanger gave vague responses about operational difficulties they were encountering. In 1939, word reached Army headquarters about a brilliant new cipher machine designed by the Navy, the ECM Mark II. Designed by none other than Joseph Winganger himself. The machine was revolutionary.
It used one rotor machine to control another rotor machine. It was Sigaba. Exact same design, exact same concept. Was Winganger actually claiming he’d invented the machine? Historical records suggest not. What actually happened was far more sophisticated and far more important. Behind the scenes, highlevel officials in both the Army and Navy were secretly coordinating.
They understood that having both services use the same encryption system was strategically vital. They needed operational compatibility. They needed standardized procedures. They needed shared logistics, but they also needed to navigate the fierce pride and institutional rivalry of both organizations. Neither service would happily accept the other guy’s machine.
So, they executed a brilliant bit of political theater. The Navy would officially adopt the ECM Mark II. The Army would officially adopt the Sagaba. Everyone in the no understood they were identical machines, but officially each service had its own system. The strategy worked.
For the first time in American military history, the Army and Navy would operate the same high-level encryption system, but they still needed to adapt the design to each services unique operational requirements. The Navy operated on ships with 24-volt electrical systems. The army needed 115V systems. So production split. Half the machines were manufactured for 24 volts, half for 115 volts.
The Navy worried about losing electrical power during combat and added an attachable hand crank so operators could manually power the machine. The Army worried about the machines being captured if positions were overrun. Their solution was characteristically aggressive. Strap a 40 lb thermite bomb to every machine. If capture appeared imminent, pull the igniter and the machine would be completely obliterated in a shower of molten metal burning at 4,000° F.
When Navy officers learned about the thermite bombs, they politely declined to add them to their shipboard machines. They felt that a 40 lb incendiary device was needlessly dangerous in confined spaces of a warship, but they graciously allowed the army to do whatever made them feel comfortable. Production began in 1940.
By August 1941, Sigaba was operational. 3 months later, everything changed. December 7th, 1941, Pearl Harbor, Hawaii. The Japanese surprise attack destroyed or severely damaged eight battleships, three cruisers, three destroyers, and 188 aircraft. Over 2400 Americans died. But buried in that catastrophe was an unexpected logistical benefit for American cryptographic operations.
The Navy had manufactured hundreds of Sigaba machines designated for specific ships. Each machine was configured, tested, and prepared to delivery to its assigned vessel. When ships were destroyed at Pearl Harbor, their assigned Sagaba machines were still in storage, waiting to be installed. The interervice cooperation that had seemed like mere bureaucratic maneuvering now proved strategically brilliant.
Because the Army and Navy used identical machines with only minor voltage differences, those surplus Navy machines could be rapidly transferred to Army units. Within weeks, 100 Pearl Harbor surplus machines were shipped to Army commands. Many would eventually see service in North Africa, protecting the communications that coordinated Operation Torch and the subsequent campaigns against Raml’s Africa Corps.
Meanwhile, production ramped up dramatically. And this is where an often overlooked group of women made an extraordinary contribution to American cryptographic security. As more and more men shipped overseas, the women accepted for volunteer emergency service, waves, became the only personnel trusted to assemble the most critical components of SIGABA, the rotors themselves.
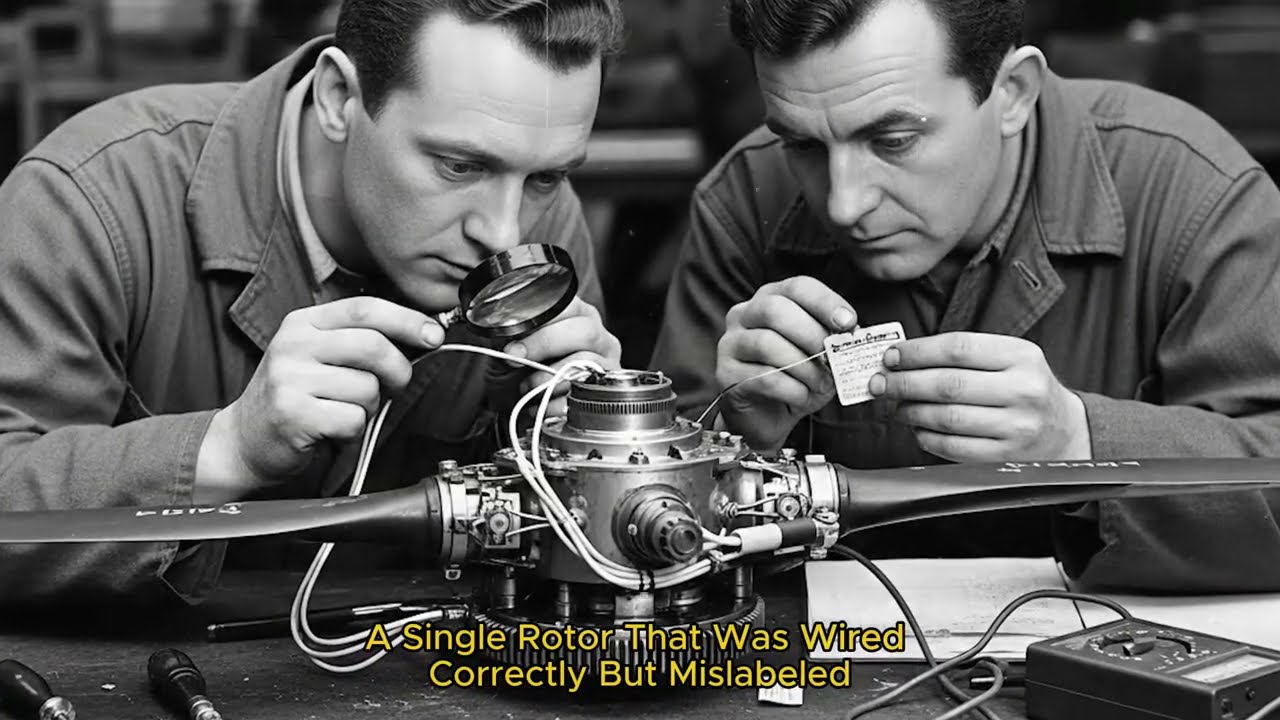
Each rotor required incredibly precise wiring. A rotor had 26 contacts on each face. 26 on the right side, 26 on the left side. Wires ran through the interior of the rotor, connecting each right side contact to a specific left side contact in a scrambled pattern. The scrambling had to be precise according to exact specifications.
A single error made the rotor useless and could potentially compromise entire networks if installed. The Waves didn’t just assemble these rotors faster than the soldiers they replaced. They doubled the production rate per person. More remarkably, over the course of the entire war, these women made exactly one documented error.
A single rotor that was wired correctly but mislabeled. One error out of 450,000 rotors. Each rotor was tested approximately 3,000 times before being approved for operational use. The regime was exhaustive, checking every possible electrical path, verifying alignment, confirming the wiring matched the specification precisely.
By the war’s end, 10,60 Sagaba machines had been produced, supported by those 450,000 individually handwired rotors. These machines carried the most sensitive Allied communications, D-Day invasion plans, Pacific theater operations against Japan, coordination of strategic bombing campaigns, diplomatic negotiations, and crucially, they protected the POS Prime communications link, the secure channel between President Franklin Roosevelt in Washington and Prime Minister Winston Churchill in London.
But with thousands of machines deployed worldwide, absolute security required more than just complex engineering. It required obsessive operational security. American military intelligence had learned crucial lessons from watching other nations cryptographic failures. The Germans had built the Enigma machine with strong mathematical foundations, but careless operating procedures had given Allied codereakers the openings they needed.
Polish mathematicians and later British crypton analysists at Bletchley Park didn’t break Enigma purely through mathematical brilliance. They exploited systematic operational errors by German operators. German military messages often began with predictable phrases. Hile Hitler or to the tank group for panzer divisions or nothing to report from scouts.
These cribs, known fragments of plain text, gave codereers starting points for decryption attacks. German operators frequently selected lazy, predictable key settings. One infamous operator always used CIL, his girlfriend’s nickname, as his message key. Allied codereers called messages encrypted with his keys sillies and could often decrypt them quickly.
Worst of all, operators would sometimes send slightly different versions of the same message using the same encryption key. Crypt analysists could compare the two encrypted texts and use the differences to work backwards to the key. American cryptographers were determined not to make the same mistakes.
First principle, never let the machine be captured. Every Sagaba station had 24-hour armed guards. Not recommended, not suggested, mandatory. Armed soldiers guarded the machines around the clock with explicit orders to destroy them rather than allow capture. Allied nations, even close allies like the British, Canadians, and Australians were not permitted direct access to Sagaba machines or detailed descriptions of how they functioned.
The Allies developed a modified version called the combined cipher machine CCM for secure interalied communication. But even that revealed minimal details about Sigaba’s internal workings. And then there was the army’s 40 lb thermite bomb. If a position appeared about to be overrun, operators had clear instructions.
Activate the thermite igniter and evacuate. Within seconds, the machine would be consumed by 4,000 degree molten metal that would melt through the rotors, the wiring, the housing, everything, leaving only a puddle of fused slag. Second principle, never allow predictable settings. The Germans let operators choose their own daily key settings, which led to the silly problem.
American cryptographers built a completely separate machine whose sole purpose was generating pseudo random daily settings for sagaba operations. These settings were printed on compact sheets 1 month’s worth of settings fit on a single piece of paper. This minimized the risk of units running out of key material and being forced to reuse old settings.
instructions specifically reminded operators to change the message key even when retransmitting the same message. Never send different content with the same key. The engineers had determined that certain message key combinations were easier to set up than others simply due to the physical design of the machine.
Those easier to set combinations were specifically listed as forbidden. Operators were instructed never to use them precisely because they were easier. To maximize the possible key combinations without adding logistical complexity, the rotors could be installed in reverse orientation. Each rotor could be inserted either normal or reversed, effectively doubling the number of possible configurations.
Third principle, verify, verify, verify. Captured enemy prisoners of war were carefully interrogated with specific questions designed to reveal whether they’d ever seen evidence that American high-level codes had been broken. German and Japanese intelligence services were monitored as carefully as possible.
Were they behaving as though they could read American strategic communications? Were their responses consistent with having advanced knowledge of allied plans? The conclusion repeatedly confirmed throughout the war. Neither Germany nor Japan was making any progress at all against Sagaba. Modern cryp analysis confirms this. The Sagaba key space, the total number of possible initial settings was approximately 100 bits.
That’s similar to early modern computer ciphers and actually stronger than the NSA’s later DEES cipher from the 1970s. But the real test came in February 1945 when the nightmare scenario nearly became real. February 3rd, 1945, Kmar, France. The city had been liberated from German occupation just days earlier.
Enemy forces were still only 4 miles to the north. The 28th Infantry Division was in the process of establishing new headquarters in the city. A 2.5 ton truck arrived carrying spare cryptographic equipment, including a complete Sagaba machine with its rotors and key lists, all secured in two locked safes. The truck parked on Barbarasa Strasa Street for the night.
The signal company’s motorpool section, which had the responsibility for establishing guarded vehicle parks, hadn’t arrived yet, so the truck sat unguarded. The next morning, February 4th, when two officers went to make repairs, the truck was gone. Within hours, the disappearance triggered a full-blown cryptographic emergency.
General Eisenhower himself became personally involved. The Supreme Allied Commander in Europe gave top priority to recovering the truck. The implications were staggering. That Sagaba machine had encrypted every detail of Allied plans for the final spring offensive into Germany. It had encrypted arrangements for President Roosevelt’s trip to the Yaltta conference.
It was the only highly secure cipher system available to many US units in Europe. If the Germans captured that machine and its associated materials, they could potentially read every high-level Allied communication encrypted with Sagaba in the entire European theater. On February 6th, headquarters issued an urgent message suspending use of all affected cryptographic systems.
Reserve systems were hastily distributed. Secure landlines and couriers replaced radio communications wherever possible. Searches intensified. Air reconnaissance flights photographed thousands of square miles. Ground patrols checked every barn, shed, and wooded area. Every unit was ordered to inventory all 2.5ton trucks and inspect their contents.
The theaterwide truck inventory turned up six 2.5 ton vehicles found in possession of the wrong units. Apparently, stealing trucks from frontline positions was common practice, but none of them was the missing cryptographic truck. Days stretched into weeks. No trace of the truck or the safes.
Investigators began developing theories. Several incidents suggested French units might have been responsible. French soldiers had been caught appropriating American vehicles in other instances. But another possibility was far more ominous. German forces had captured American soldiers from the 28th Division in the days before February 5th.
They could have learned about the cryptographic equipment and organized a special operation to capture it. Finally, on March 9th, 34 days after the theft, the truck was found abandoned in woods near Rumbar Villairs, about 45 mi northeast of Kmar. The bumpers had been removed and serial numbers painted over, but the truck was otherwise intact.
The safes were gone. That same afternoon, French searchers found one of the safes submerged in the Gresen River near a bridge between Shenoa and Sherwiller. When opened, it contained the Sagaba machine itself. Cryptographic experts conducted immediate inspection. The crucial question, had the machine been compromised? The rotor settings were still configured for February 5th, the day after the theft.
This was actually a security violation. Rotors were supposed to be removed when transporting machines, but it also suggested the thieves hadn’t tampered with the settings. The safe’s combination lock showed no evidence of tampering. The mud and water damage made fingerprinting impossible, but experts concluded the safe probably hadn’t been opened.
11 days later, on March 20th, the second safe was recovered from the riverbed about 100 ft downstream from the bridge. They tried to open it immediately, but the combination lock was clogged with silt. So, the safe was sent to Paris for opening at a ceremony attended by what one officer later described as half of the intelligence staff in Paris.
They attempted to cut it open with a torch. Fortunately, the torch ran out of oxygen after cutting about 2 in. Fortunately, because when they finally cut and drilled the safe open that late evening, long after the VIP guests had departed, they discovered it contained two 55 lb thermite bombs and 14lb blocks of TNT, all wired to detonators.
If the torch had cut through another inch or two while the VIPs watched, the explosives were the standard destruction devices carried with cipher machines. They weren’t booby traps designed to kill whoever opened the safe, but they could certainly have killed the entire audience if triggered accidentally. [snorts] Investigations eventually revealed what actually happened.
Two French peasants told authorities an acquaintance, a farmer, had taken the truck to move his household furniture. When the investigation began and the farmer realized the severity of the theft, he panicked and dumped the safes in the river. The thieves had no idea the truck contained the most sensitive cryptographic equipment in the Allied arsenal. They just wanted the truck.
The consensus was no compromise had occurred. The machine and materials had never fallen into enemy hands. But the incident demonstrated how vulnerable even the most secure cryptographic systems were to simple theft and operational mistakes. SIGABA continued protecting American military communications long after the war ended.
It remained in operational service until the 1960s, 15 years after the defeat of Germany and Japan. It was finally declassified in 1996, more than 50 years after its operational debut. To this day, there is no verified evidence that German or Japanese crypt analysts ever made any meaningful progress against Sagaba.
Modern computer-based crypt analysis using techniques impossible during World War II can eventually break Sagaba, but it requires enormous computational resources and is only practical if you have multiple messages encrypted with the same key settings. The engineering principles that made Sagaba successful remain relevant today.
First, complexity is essential, but it must be manageable complexity. Sagaba’s 15 rotors in three banks created extraordinary cryptographic strength, but the machine could still be operated by trained personnel in field conditions. Second, operational security matters as much as mathematical security. Enigma’s mathematical foundation was strong, but operational mistakes made it vulnerable.
Sigaba’s designers obsessively addressed operational security from the beginning. Third, interervice and inter agency cooperation, even when politically difficult, produces better outcomes than isolated development. The army navy coordination that produced Sagaba required overcoming substantial institutional rivalry, but it resulted in a system that served both organizations superbly.
Fourth, manufacturing precision is critical for cryptographic security. The Waves who assembled 450,000 rotors with only one documented error understood they weren’t just assembling machines. They were protecting lives and securing victory. Modern encryption operates on entirely different principles. We use mathematical algorithms implemented in software rather than mechanical rotors.
But the lessons remain strong design, obsessive operational security, careful manufacturing, and institutional cooperation. When you send an encrypted message today, whether it’s a banking transaction, a classified military communication, or just a private message to a friend, you’re relying on principles that engineers like William Freriedman and Frank Rowlet pioneered over 90 years ago.
The machines are gone. The 10,60 Sagaba devices were eventually decommissioned and mostly destroyed. A few survive in museums, silent monuments to the cryptographers, engineers, and waves who built them. But the fundamental insight remains. Security doesn’t come from keeping your methods secret. It comes from building systems so complex that even enemies who fully understand how they work still can’t break them without the keys.
That was the secret of Sagaba. Not the 15 rotors, not the complex stepping patterns, not even the 100 bit key space. The real secret was engineering a system where everything could be known, the design, the mechanisms, the principles, and it still couldn’t be broken. That’s the difference between security through obscurity and security through design.
And it’s why Sigaba remains the only major cipher machine of World War II that was never defeated by enemy codereers. From a frustrated cryptographer threatening to quit in 1934 to women assembling rotors with extraordinary precision to a stolen truck that nearly changed the course of the war. The story of Sagaba is the story of engineering excellence under pressure.
It’s proof that the best solutions often come from team members willing to challenge authority. That manufacturing precision matters as much as design brilliance. And that sometimes the most important contribution to history is building something so secure that its story can only be told 50 years later. If you found this technical problem-solving story fascinating, you’ll want to explore more about wartime communication innovations.
The story of how Allied forces coordinated D-Day using radio networks designed to resist German jamming. Or how prisoners of war built radio receivers from scavenged parts to secretly listen to BBC broadcasts. Those stories reveal the same engineering creativity under impossible constraints. Hit that subscribe button and bell icon so you don’t miss these deep dives into the technical problems that shaped history.
Drop a comment telling me what other wartime communication or engineering challenges would you like to see explained. Because the best stories in military history aren’t about who won the battles. They’re about how engineers solved the seemingly impossible problems that made victory possible.
Note: Some content was generated using AI tools (ChatGPT) and edited by the author for creativity and suitability for historical illustration purposes.